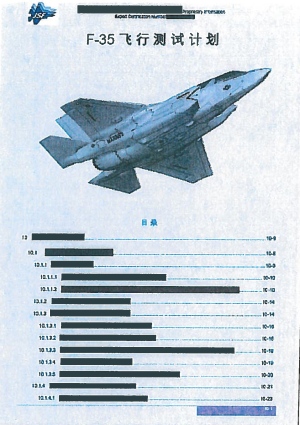
This image shows a page of the flight test plan for the F-35, the world’s most advanced multi-role fighter aircraft, from an internal company document that Su Bin allegedly acquired and translated before passing on to contacts in China.
(Globe and Mail) A Chinese man accused of being the “directing mind” behind a corporate-espionage conspiracy to steal jet-fighter secrets from Pentagon contractors is a Canadian immigrant who is being stripped of his residency status.
Su Bin, 48, a Beijing businessman with a home in Vancouver, will find out in a B.C. court on Wednesday whether he will get bail. U.S. officials allege he gave instructions to hackers in China that helped them zero in on which secrets to steal from the computers of Boeing Co. and other firms for the benefit of Chinese aviation companies.
The FBI allegations against Mr. Su, which were made public earlier this month, concern intercepted e-mail conversations dating back to 2009 with two professional computer hackers in China. He is charged with conspiring to gain unauthorized access to a protected computer.
The allegations highlight a growing fear among intelligence officials that North America’s military and industrial edge is being dulled by immigrants who are accepted as legitimate professionals but seek profit in illegally moving secrets overseas. . . . (read more)
FBI: We found US MILITARY AIRCRAFT INTEL during raid on alleged Chinese hacker (Register)
A Chinese entrepreneur has been arrested for attempting to steal information on the United States’ Lockheed F-22 and F-35 aircraft and Boeing’s C-17 cargo plane.
Su Bin – along with two uncharged Chinese co-conspirators – is alleged to have hacked into Boeing’s corporate network as well as those of defence contractors in the US and Europe, to gain information the accused said in an email would help China “stand easily on the giant’s shoulders”.
Su, who had previously operated Chinese aviation firm Lode Technologies, is alleged to have broken into the Boeing network on January 2010, according to a report within a federal complaint unsealed in Los Angeles this week. The suspect and his “co-conspirators” are also alleged to have hacked the systems of other US defence contractors between 2009 and 2013 from a location in China.
The group was alleged to have stolen gigabytes of data on 32 US projects, including what investigators believed was 220MB relating to the F-22.
“Emails between SU and (a co-conspirator) in January 2010 contain at least one lengthy C-17 directory file listing that matches in extensive detail the files and folders hosted on Boeing’s computer systems,” FBI special agent Noel Neeman wrote.
“These facts show that the C-17 data was ex-filtrated directly from Boeing’s computer systems.” . . .
Su Bin, accused by FBI of hacking, denied bail in Vancouver (CBC)
A judge has refused bail for a Chinese citizen who owns a home in Vancouver and is accused by U.S. authorities of leading a sophisticated scheme to steal military secrets.
B.C. Supreme Court Justice Austin Cullen ordered the continued detention of Su Bin, whose permanent residency in Canada was revoked as he faces possible extradition to the U.S.
The FBI alleges Su was the mastermind of a plot to electronically steal information from American military contractor Boeing and sell it to companies in China . . .
Corporate spying case reveals details of sophisticated system (Globe and Mail)
The case of a Chinese entrepreneur accused of directing an effort to steal secrets about the Pentagon’s jet-fighter technology sheds new light on how foreign hackers cover their tracks, and why Canada feels it may be necessary to invade people’s privacy to stop them.
U.S officials have charged Beijing-based businessman Su Bin, an aerospace engineer with permanent residency status in Canada, of directing an espionage conspiracy in which he told two China-based hackers how to infiltrate the computer systems of Boeing Co. and other military contractors.
Documents filed as part of a U.S. bid to extradite the 48-year-old do not name the foreign hackers, but the case’s intercepted e-mails highlight the mechanics of modern espionage.
Court documents filed in the extradition case say the hackers created a global network of compromised computers that served as a traceless conveyor belt for stolen secrets.
“In order to avoid diplomatic and legal complications, surveillance work and intelligence collection are done outside China,” the court documents quote the hackers as saying in an e-mail exchange.
E-mails in the court filings show the two unnamed hackers frequently discussed best practices, including their strategy of relaying cyberattacks through a series of computers they infiltrated in several countries. Such infected computers are referred to by information technology experts as “hop points.”
“A hop point is used to conceal the true origin of commands being sent to a victim computer,” reads a U.S. government affidavit in the case.
The documents say the hackers set up a hop-point pathway involving computers in Singapore, Korea and, finally United States, so that the attacks would have appeared to have had a U.S. origin.
The documents say stolen data were similarly routed to servers in Hong Kong or Macao. Data allegedly passed from hand to hand after that: “The intelligence is always picked up and transferred to China in person.” . . . .(read more)