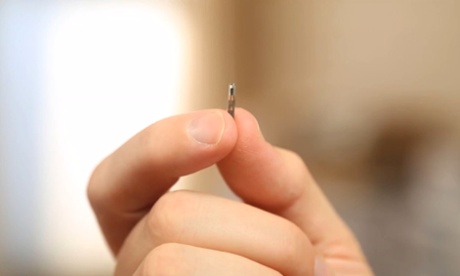
(Forbes) US navy petty officer Seth Wahle, now an engineer at APA Wireless, implanted a chip in his hand, in between the thumb and the finger of his left hand. It has an NFC (Near Field Communications) antenna that pings Android phones, asking them to open a link. Once the user agrees to open that link and install a malicious file, their phone connects to a remote computer, the owner of which can carry out further exploits on that mobile device. Put simply, that Android device is compromised. . . .
. . . He’ll be showing off the surreptitious attack at the Hack Miami conference taking place this May, alongside the event’s secretary of the board and security consultant Rod Soto. They admit it’s a rather crude piece of research, given it’s using off-the-shelf tools and a known attack technique over NFC, but claim this implant-based attack could provide criminals with a particularly useful “tool in their social engineering toolset”.
And, at a time when airlines and federal agencies are cracking down anyone even thinking about testing the security of in-flight communications systems, implantable chips provide a clever way to sneak electronics past checks at airports or other high-security locations. Wahle says he put the chip in when he was still employed by the military and it was never detected despite going through scanners every day. “They would have to put me through the X-ray [if they were going to detect the chip].”
“This implanted chip can bypass pretty much any security measures that are in place at this point and we will show proof of that,” says Soto.
Looking at the widespread adoption of NFC in business, implants could provide a route into various networks. More sophisticated code on the chip would increase the potential for more serious damage, especially if a zero-day (an unpatched, previously-unknown vulnerability) was put into action via a chip, warns Soto. . . .(read the rest)