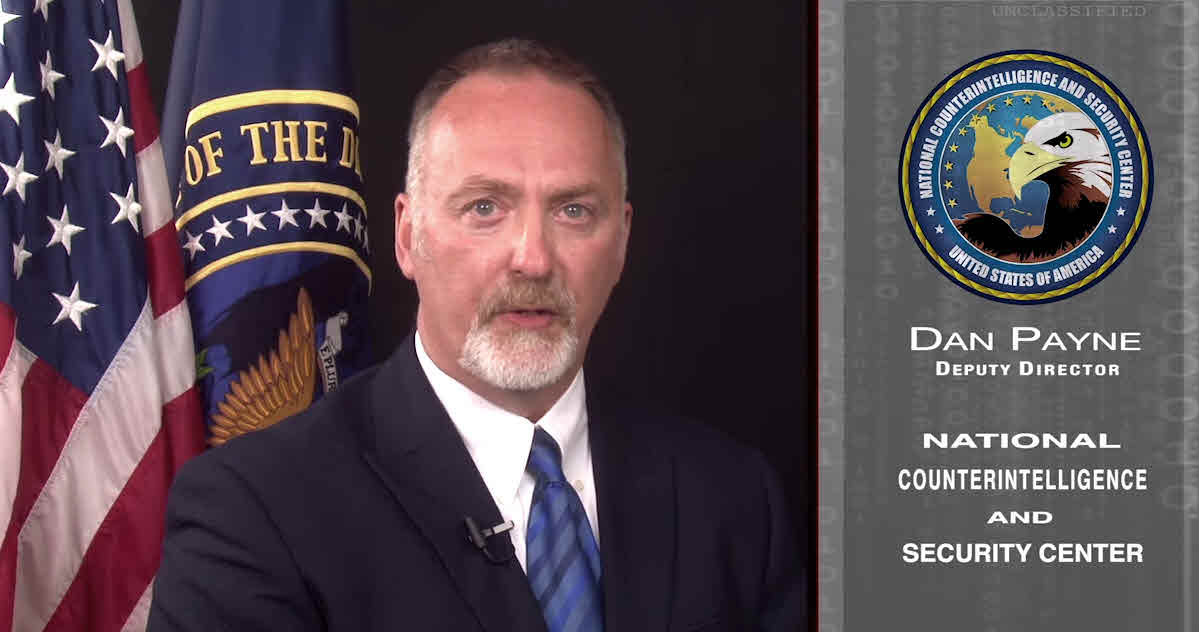
“Some of you may think that you are not of interest because you don’t have access to classified information. You are mistaken.” —Deputy National Counterintelligence Executive Dan Payne
After hacking, government workers warned of potential fraud (AP)
An immense hack of millions of government personnel files is being treated as the work of foreign spies who could use the information to fake their way into more-secure computers and plunder U.S. secrets.
Federal employees were told in a video Friday to change all their passwords, put fraud alerts on their credit reports and watch for attempts by foreign intelligence services to exploit them. That message came from Dan Payne, a senior counterintelligence official for the Director of National Intelligence.
“Some of you may think that you are not of interest because you don’t have access to classified information,” he said. “You are mistaken.”
Federal officials said Friday the cyberattack appeared to have originated in China, but they didn’t point fingers directly at the Chinese government. The Chinese said any such accusation would be “irresponsible and unscientific.”
“We know that the attack occurred from somewhere in China, but we don’t know whether it was an individual or a group or a nation-state attack,” said Rep. Jim Langevin, a Rhode Island Democrat and leading voice in Congress on cybersecurity. He added, though that it had “all the hallmarks of a nation-state attack.”
White House spokesman Josh Earnest said he couldn’t divulge much while the case was under investigation. Still, he noted that investigators “are aware of the threat that is emanating from China.”
One U.S. official said the breach of data involving more than 4 million past and present federal workers was being investigated as a national security matter. That suggests authorities believe a nation was behind it rather than a more loosely organized gang of cybercriminals. The official was not authorized to discuss an ongoing investigation and spoke only on condition of anonymity.
The breach was an embarrassing showing for the U.S. government’s vaunted computer-defense system for civilian agencies — dubbed “Einstein” — which is costing $376 million this year alone. It’s supposed to detect unusual Internet traffic that might reflect hacking attempts or stolen data being transmitted outside the government.
A wide range of information is prized by spies — classified military secrets but also economic strategy and internal foreign policy debates.
This latest breach occurred in December but wasn’t discovered until April, officials say. It was made public Thursday.
“The scale of it is just staggering,” said Rep. Adam Schiff, D-Calif., top Democrat on the House Intelligence Committee. There’s no telling how many more attacks could be spawned by the information stolen in this case, he said.
Although most Americans think of identity thieves stealing from credit card or bank accounts, the information about civilian federal workers has other value for spies.
“They’re able to identify people who are in positions with access to significant national security information and can use personal data to target those individuals,” said Payne, the counterintelligence official.
He said details from personnel files could be used to craft personalized phony messages to trick workers. Federal employees who think they’re opening an email from co-workers or family members might infect their computers with a program that would steal more information or install spy software.
Spies also could use details about an employee’s interests or background to befriend them and try to manipulate them into revealing secrets.
Kevin Mitnick, a former hacker who now runs Mitnick Security Consulting of Las Vegas, called confidential details about federal employees “a gold mine.”
“What’s the weakest link in security?” Mitnick said. “The human. Now you know all about your target.”
The hackers may have made off with even more information about workers who undergo security clearance background checks. That information includes the names of family, neighbors, even old bosses and teachers, as well as reports on vices, arrests and foreign contacts.
However, OPM spokesman Samuel Schumach said there was no evidence to suggest that security clearance information collected by OPM was compromised. It’s stored separately from routine personnel files, he said.
“The kind of data that may have been compromised in this incident could include name, Social Security Number, date and place of birth, job assignments, training files, performance ratings and current and former addresses,” Schumach said in an email.
The breach occurred at a network maintained by the Department of Interior, which also houses the personnel agency’s files. Schumach said agencies share computer systems partly to save money — and it’s also supposed to strengthen security.
Security experts said the hackers may have gone after the personnel agency because it’s an easier target than the Pentagon or National Security Agency.
Private cybersecurity researchers said they believe the personnel agency was targeted by the same hackers who got into the Anthem and Primera health insurance groups last year.
John Hultquist, head of cyberespionage intelligence at iSight, said the Dallas-based security firm had found evidence linking the insurance and government attacks, but declined to say whom they suspect. “We think they are creating a database they can leverage for follow-on espionage,” Hultquist said. . . . (read more)
With a series of major hacks, China builds a database on Americans (Washington Post)
China is building massive databases of Americans’ personal information by hacking government agencies and U.S. health-care companies, using a high-tech tactic to achieve an age-old goal of espionage: recruiting spies or gaining more information on an adversary, U.S. officials and analysts say.
Groups of hackers working for the Chinese government have compromised the networks of the Office of Personnel Management, which holds data on millions of current and former federal employees, as well as the health insurance giant Anthem, among other targets, the officials and researchers said.
“They’re definitely going after quite a bit of personnel information,” said Rich Barger, chief intelligence officer of ThreatConnect, a Northern Virginia cybersecurity firm. “We suspect they’re using it to understand more about who to target [for espionage], whether electronically or via human recruitment.”
The targeting of large-scale databases is a relatively new tactic and is used by the Chinese government to further its intelligence-gathering, the officials and analysts say. It is government espionage, not commercial espionage, they say.
“This is part of their strategic goal — to increase their intelligence collection via big-data theft and big-data aggregation,” said a U.S. government official who, like others, spoke on the condition of anonymity to discuss a sensitive topic. “It’s part of a strategic plan.” . . . (read more)
Hackers May Have Obtained Names of Chinese With Ties to U.S. Government (New York Times)
Investigators say that the Chinese hackers who attacked the databases of the Office of Personnel Management may have obtained the names of Chinese relatives, friends and frequent associates of American diplomats and other government officials, information that Beijing could use for blackmail or retaliation.
Federal employees who handle national security information are required to list some or all of their foreign contacts, depending on the agency, to receive high-level clearances. Investigators say that the hackers obtained many of the lists, and they are trying to determine how many of those thousands of names were compromised.
In classified briefings to members of Congress in recent days, intelligence officials have described what appears to be a systematic Chinese effort to build databases that explain the inner workings of the United States government. The information includes friends and relatives, around the world, of diplomats, of White House officials and of officials from government agencies, like nuclear experts and trade negotiators. . . . (read more)
Records from government data breach surface on ‘darknet,’ says expert (Fox News)
OPM data breach could expose troops, clearance holders (C4ISR)
OPM hack: What criminal hackers can do with your personal data (CSM)
OPM records the ‘Holy Grail’ of counterintelligence (FCW)
– – –
Information About the Recent Cybersecurity Incident
June 4, 2015
Office of Personnel Management
Announcement
The U.S. Office of Personnel Management (OPM) recently became aware of a cybersecurity incident affecting its systems and data that may have compromised the personal information of current and former Federal employees.
Within the last year, OPM has undertaken an aggressive effort to update its cybersecurity posture, adding numerous tools and capabilities to its networks. As a result, in April 2015, OPM became aware of the incident affecting its information technology (IT) systems and data that predated the adoption of these security controls.
Since the incident was identified, OPM has partnered with the U.S. Department of Homeland Security’s U.S. Computer Emergency Readiness Team (US-CERT), and the Federal Bureau of Investigation to determine the impact to Federal personnel. And OPM immediately implemented additional security measures to protect the sensitive information it manages.
Beginning June 8 and continuing through June 19, OPM will be sending notifications to approximately 4 million individuals whose Personally Identifiable Information was potentially compromised in this incident. The email will come from [email protected] and it will contain information regarding credit monitoring and identity theft protection services being provided to those Federal employees impacted by the data breach. In the event OPM does not have an email address for the individual on file, a standard letter will be sent via the U.S. Postal Service.
In order to mitigate the risk of fraud and identity theft, OPM is offering affected individuals credit monitoring services and identity theft insurance with CSID, a company that specializes in identity theft protection and fraud resolution. This comprehensive, 18-month membership includes credit report access, credit monitoring, identity theft insurance, and recovery services and is available immediately at no cost to affected individuals identified by OPM.
Additional information is available beginning at 8 a.m. CST on June 8, 2015 on the company’s website, www.csid.com/opm (external link), and by calling toll-free 844-222-2743 (International callers: call collect 512-327-0700).
Steps for Monitoring Your Identity and Financial Information
- Monitor financial account statements and immediately report any suspicious or unusual activity to financial institutions.
- Request a free credit report at www.AnnualCreditReport.com (external link) or by calling 1-877-322-8228. Consumers are entitled by law to one free credit report per year from each of the three major credit bureaus – Equifax®, Experian®, and TransUnion® – for a total of three reports every year. Contact information for the credit bureaus can be found on the Federal Trade Commission (FTC) website, www.ftc.gov (external link).
- Review resources provided on the FTC identity theft website, www.identitytheft.gov (external link). The FTC maintains a variety of consumer publications providing comprehensive information on computer intrusions and identity theft.
- You may place a fraud alert on your credit file to let creditors know to contact you before opening a new account in your name. Simply call TransUnion® at 1-800-680-7289 to place this alert. TransUnion® will then notify the other two credit bureaus on your behalf.
Precautions to Help You Avoid Becoming a Victim
- Be suspicious of unsolicited phone calls, visits, or email messages from individuals asking about you, your employees, your colleagues or any other internal information. If an unknown individual claims to be from a legitimate organization, try to verify his or her identity directly with the company.
- Do not provide personal information or information about your organization, including its structure or networks, unless you are certain of a person’s authority to have the information.
- Do not reveal personal or financial information in email, and do not respond to email solicitations for this information. This includes following links sent in email.
- Do not send sensitive information over the Internet before checking a website’s security (for more information, see Protecting Your Privacy, www.us-cert.gov/ncas/tips/ST04-013 (external link)).
- Pay attention to the URL of a website. Malicious websites may look identical to a legitimate site, but the URL may use a variation in spelling or a different domain (e.g., .com vs. .net).
- If you are unsure whether an email request is legitimate, try to verify it by contacting the company directly. Do not use contact information provided on a website connected to the request; instead, check previous statements for contact information. Information about known phishing attacks is also available online from groups such as the Anti-Phishing Working Group (www.antiphishing.org (external link)).
- Install and maintain anti-virus software, firewalls, and email filters to reduce some of this traffic (for more information, see Understanding Firewalls, www.us-cert.gov/ncas/tips/ST04-004 (external link); Understanding Anti-Virus Software, www.us-cert.gov/ncas/tips/ST04-005 (external link); and Reducing Spam, http://www.us-cert.gov/ncas/tips/ST04-007 (external link)).
- Take advantage of any anti-phishing features offered by your email client and web browser.
- Employees should take steps to monitor their personally identifiable information and report any suspected instances of identity theft to the FBI’s Internet Crime Complaint Center at www.ic3.gov(external link).
- Additional information about preventative steps by consulting the Federal Trade Commission’s website, www.identitytheft.gov (external link). The FTC also encourages those who discover that their information has been misused to file a complaint with the commission using the contact information below.
Identity Theft Clearinghouse
Federal Trade Commission
600 Pennsylvania Avenue, NW
Washington, DC 20580
www.identitytheft.gov
1-877-IDTHEFT (438-4338)
TDD: 1-202-326-2502