Former TVA manager admits Chinese government paid him for nuclear secrets (Knoxville News Sentinel)
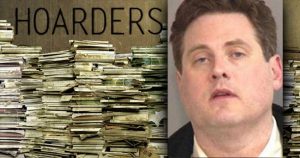
A former senior TVA manager has admitted he was paid by the Chinese government for nuclear technological information while working for the utility, court records unsealed Friday show.
Ching Ning Guey has struck a deal to plead guilty to a charge of development of special nuclear material outside the U.S. The case, kept under seal for more than a year, is tied to an indictment announced earlier this month against a Chinese nuclear engineer and a Chinese-owned nuclear power plant alleging nuclear espionage.
Guey worked as a senior manager for the probabilistic risk assessment division of the Tennessee Valley Authority from 2010 to 2014. According to a plea agreement filed by Assistant U.S. Attorney Charles Atchley, Guey had access through his job to tightly-controlled information about the development and production of special nuclear material.
“The defendant received warnings and guidance on the restrictions and controls that pertain to the prohibitions against the distribution and sharing of this information with restricted countries,” Atchley wrote.
But in November 2013, Guey was invited to travel to China at the request of a nuclear power company owned by the People’s Republic of China. The trip was financed by the Chinese government, and Guey was paid by the Chinese government for three key Electric Power Research Institute reports that China was barred from accessing, Atchley wrote. All three reports provided key information about light-water and heavy-water nuclear reactors and are regulated by the U.S. Department of Energy’s National Nuclear Security Administration Office of Nonproliferation and International Security.
Guey, who was born in Taiwan but became a naturalized citizen in 1990, was recruited as far back as 2004 to provide the Chinese government with nuclear information, court records show. That relationship came as a result of Guey’s meeting in the early 1990s with Chinese nuclear engineer Szuhsiung “Allen” Ho at a Chinese American Nuclear Technology Association event. . . . (read more)
CHINESE SPY IN FLORIDA SENT DRONE PARTS TO CHINA FOR MILITARY (Newsweek)
A Chinese woman living in Florida was a spy who smuggled underwater drone parts from U.S. companies to a state-owned university in China that does military research—the latest example of economic espionage, which the FBI says has increased by over 50 percent—according to federal prosecutors on Thursday.
Amin Yu, 53, worked as a researcher at Harbin Engineering University studying “underwater remotely operated vehicles” until she came to the U.S. in 1998, according to her 18-count indictment.
Yu used two companies she started to buy systems and components for underwater vehicles under the direction of a Harbin professor between 2002 and 2014. She then sent the parts to China, where the professor and other co-conspirators used them to develop drones for the Navy of the People’s Liberation Army and other state entities, the indictment states.
Yu, a Chinese citizen living in Orlando as a permanent resident and working part-time at a university there, allegedly bought parts like cables and connectors, video guidance computers and underwater acoustic locater devices. She purchased the parts from companies in the U.S., Canada and Europe, and sent them to China using the United States Postal Service and UPS, while filing bogus export forms that didn’t mention the parts were headed for Harbin Engineering University, according to the indictment.
Yu was charged with conspiracy, acting in the U.S. as the illegal agent of a foreign government, money laundering and filing false export information, according to the U.S. Department of Justice. The case is being prosecuted by attorneys from the DOJ’s national security division.
Another Chinese citizen, Fuyi Sun, was arrested last week in New York City after he allegedly traveled from China and paid undercover federal agents tens of thousands of dollars for carbon fiber he said was headed to the Chinese military. . . . (read more)
Security of critical phone database called into question (Washington Post)
Federal officials fear that national security may have been jeopardized when the company building a sensitive phone-number database violated a federal requirement that only U.S. citizens work on the project.
The database is significant because it tracks nearly every phone number in North America, making it a key tool for law enforcement agencies seeking to monitor criminal or espionage targets.
Now Telcordia, a Swedish-owned firm, is being compelled to rewrite the database computer code — a massive undertaking — to assuage concerns from officials at the FBI and Federal Communications Commission that foreign citizens had access to the project. These officials fear that if other countries gain access to the code, they could reap a counterintelligence bonanza, learning the targets of U.S. law enforcement and espionage investigations.
The security rewrite began in March after the agencies learned that a Chinese citizen with a U.S. work permit had helped write the system code, said individuals familiar with the matter who spoke on the condition of anonymity to discuss a sensitive matter. Seven other foreign citizens, including a British engineer, also worked on the project, although it was the Chinese engineer who raised red flags for officials. . . . (read more)
Intelligence leaders impatient for insider threat social media guidance (Federal News Radio)
Immensely complex questions of privacy and civil liberties are holding up agencies from using perhaps the most valuable sources of information they could find on current and future employees: social media and other publicly available online information.
“These things take a long time,” said Alex Joel, chief civil and privacy protection officer at the Office of the Director of National Intelligence, during an April 28 panel discussion at the Intelligence and National Security Alliance’s insider threat symposium in Chantilly, Virginia. “If there was an easy answer, we’d have it already. We’re working at the pace of government to try to figure this out.”
Social media is the “void” the National Security Agency is trying to fill with its own insider threat program, Kemp Ensor, director of security at the NSA, said. His employees don’t go home and talk to their neighbors anymore, he said. They go online.
“That’s where we need to be,” Ensor said. “That’s where we need to mine from if we’re going to build the trusted workforce of the future.” . . . . (read more)
Researchers say there are serious security problems in Samsung’s SmartThings (The Verge)
Researchers at the University of Michigan have uncovered multiple design flaws in Samsung’s SmartThings platform that could allow a malicious app to unlock doors, set home access codes, falsely set off smoke alarms, or put devices on vacation mode, among other attacks. Crucially, all the attacks require users to either install a malicious app from the SmartThings store or click a malicious link.
Multiple issues exist in SmartThings’ framework, the researchers say, but most pressing are the privileges given to apps, many of which they don’t need to function. A smart lock might only need the ability to lock itself remotely, for instance, but the SmartThings API bundles that command with the unlock command, which an attacker can leverage to carry out a physical attack.
Another over-granting of permissions involves the way in which SmartApps connect to physical devices. When a user downloads a SmartApp, it asks for specific permissions to perform its intended purpose. After being installed, SmartThings then lists all the devices that could be used with that app because of its ability to sync with those permissions. But it also gives the app more access than it needs. . . . (read more)
ISIS building Google-style driverless cars to launch bomb attacks in West (Daily Express)
Islamic State (ISIS) technicians are working flat out to develop a Google-style driverless car that could navigate itself into a crowded area before detonating an explosive device, a Nato security expert has warned.
ISIS’ research and development department in the terror group’s de facto Syrian capital, Raqqa, is believed to be producing the vehicles at the same time as US internet giant Google attempts to perfect the same technology.
If successful, the invention could prove to be a major headache for security services in Britain and throughout Europe and North America, where self-driving cars are expected to become commonplace. . . . (read more)
U.S. Steel Giant Charges That Chinese Government Stole Company Secrets (Washington Free Beacon)
U.S. Steel Corp accused the Chinese government of hacking into a company computer to steal the blueprints for new lightweight steel technology so that Beijing-based auto producers could expand their reach into America.
The Wall Street Journal reported Thursday that U.S. Steel filed a complaint with the International Trade Commission earlier this week accusing the Xi government of working on the behalf of Chinese auto companies to swipe proprietary plans for the new steel.
The Pittsburgh-based company alleges the hack infiltrated a researcher’s computer in 2011. . . . (read more)
U.S. Congress passes legislation to protect firms’ trade secrets (Reuters)
The U.S. Congress on Wednesday passed and sent to President Barack Obama legislation strengthening legal protection for companies’ trade secrets, including manufacturing processes and computer methods.
The House of Representatives voted 410-2 to approve the “Defend Trade Secrets Act” on the heels of it being unanimously passed by the Senate earlier this month.
The legislation, which is backed by the White House, would open the door for companies to sue in federal court for damages related to theft of trade secrets.
House Judiciary Committee Chairman Bob Goodlatte said the measure “will help American innovators protect their intellectual property from criminal theft by foreign agents and those engaging in economic espionage.” . . . (read more)
Chinese Cartoon Warns Against ‘Dangerous Love’ With Foreigners Who May Be Spies (NPR)
In a colorful, 16-panel cartoon called “Dangerous Love,” China is warning female government workers that romancing handsome foreigner strangers can lead to heartbreak — and espionage.
Posters seen around Beijing show a cartoon government worker named Xiao Li striking up a relationship with a bespectacled, red-haired “visiting scholar.” They share a romantic dinner and stroll through a leafy park. “Having a handsome, romantic, talented foreign boyfriend is pretty nice!” Li says to herself, according to The New York Times’ translation.
But “pretty nice” turns to nightmarish after Li’s new paramour persuades her to lend him internal government documents. Suddenly, the foreign boyfriend is nowhere to be found. Li weeps in front of two gruff police officers, who tell her she has a “shallow understanding of secrecy for a state employee,” according to The Guardian.
“Dangerous Love” was posted in Beijing’s subway and streets to mark National Security Education Day, which was “established after China passed a National Security Law in July outlining greater security efforts in 11 areas, including political, territorial, military, cultural and technological,” the Times reports.
In a statement, a district government in Beijing says that “it would display the poster to educate its employees about keeping classified information confidential and reporting to state security agencies if they spot any spying activity,” according to The Associated Press. . . . .(read more)
–